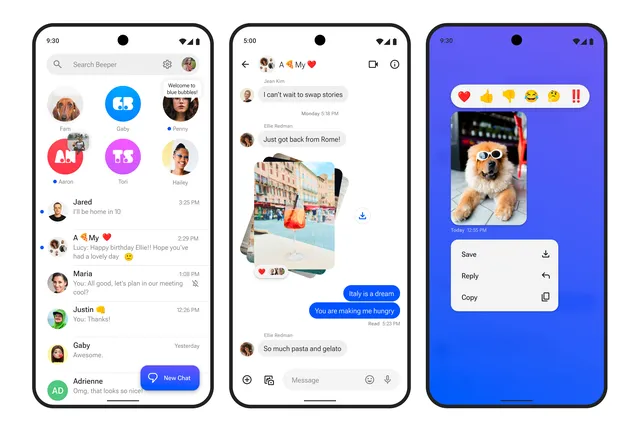
A few days after the Beeper team triumphantly unveiled a mechanism for customers to send blue-bubble iMessages directly from their Android smartphones, and roughly 24 hours after it became evident Apple had taken efforts to shut it down, Apple has offered their perspective on the problem.
The company’s response is rather predictable: it claims to be merely attempting to do the right thing by consumers by protecting the privacy and security of their iMessages. “We took steps to protect our users by blocking techniques that exploit fake credentials in order to gain access to iMessage,” said Nadine Haija, senior PR manager at Apple.
Here’s the statement in full:
At Apple, we build our products and services with industry-leading privacy and security technologies designed to give users control of their data and keep personal information safe. We took steps to protect our users by blocking techniques that exploit fake credentials in order to gain access to iMessage. These techniques posed significant risks to user security and privacy, including the potential for metadata exposure and enabling unwanted messages, spam, and phishing attacks. We will continue to make updates in the future to protect our users.
This sentence implies several things. First, Apple did indeed shut down Beeper Mini, which connects to iMessage via a custom-built service using Apple’s own push notification service — all iMessage messages transit over this protocol, which Beeper essentially intercepts and transmits to your device. Beeper had to persuade Apple’s servers that it was pinging the notification protocols from a legitimate Apple device, which it clearly wasn’t. (These are the “fake credentials” that Apple is referring to. Quinn Nelson of Snazzy Labs provided a fantastic video explaining how everything works.)
Beeper says its process works with no compromise to your encryption or privacy; the company’s documentation says that no one can read the contents of your messages other than you. But Apple can’t verify that, and says it poses risks for users and the people they chat with.
These techniques posed significant risks to user security and privacy
However, there is clearly a far larger picture at work here. “Buy your mom an iPhone,” CEO Tim Cook told a Code Conference questioner who wanted a better way to message their Android-toting mother, and the company’s executives have debated Android versions in the past but decided it would cannibalize iPhone sales. Apple has recently stated that it would embrace the cross-platform RCS messaging system, but we don’t know what that will entail — and you can bet that Apple will continue to strive to make life easier for native iMessage users.
Apple’s announcement comes at an intriguing moment. Beeper has been around for a few years, and its prior attempts to intercept iMessage were significantly more troublesome in terms of security. Beeper and applications like Sunbird (who just collaborated with Nothing on another approach to deliver iMessage to Android) were simply routing your iMessage traffic through a Mac Mini someplace in a server rack, leaving your communications far more susceptible. However, Beeper Mini directly exploited the iMessage protocol, prompting Apple to improve its security procedures.
Beeper has been working tirelessly to reactivate Beeper Mini since Apple switched it off. On Saturday, the business said that iMessage was back in the regular Beeper Cloud app, but Beeper Mini was still down. “If Apple truly cares about the privacy and security of their own iPhone users, why would they stop a service that enables their own users to now send encrypted messages to Android users, rather than using unsecure SMS?” said founder Eric Migicovsky on Friday.
Migicovsky says his position hasn’t changed after hearing Apple’s comments. He adds he’d be delighted to share Beeper’s code with Apple for a security audit so that Apple may be confident in Beeper’s security standards. Then he comes to a halt. “But I disagree with the entire premise!” Because the starting point is that iPhone users can only communicate with Android users via unencrypted messaging.”
According to Beeper, SMS is so inherently vulnerable that almost anything else would be a better. When I suggest that perhaps Apple’s issue is that iPhone users are now sending their purportedly Apple-only blue-bubble communications via a firm — Beeper — that they are unaware of, Migicovsky pauses for a moment. “That’s fair,” he adds, offering a solution: perhaps every communication received through Beeper should be preceded with a pager emoji, so people know what’s what. If that solves the problem, he claims it could be done in a matter of hours.
When I ask Migicovsky whether he’s willing to fight Apple’s security team for the foreseeable future, he argues that the fact that Beeper Cloud is still operational indicates that Apple can’t or won’t keep it out indefinitely. (He also claims that Beeper’s crew has some ideas for Beeper Mini.) Aside from that, he believes that the court of public opinion will eventually persuade Apple to play nice anyhow. “What we’ve built is good for the world,” he goes on to remark. “It’s something we can almost all agree should exist.”
Within Apple, at least this argument seems likely to fall on deaf ears. The company has kept iMessage tightly controlled and carefully secured for years, and isn’t likely to loosen the reins now. And if Beeper does ever get Beeper Mini working again, it’s destined for a never-ending game of cat and mouse trying to stay one step ahead of Apple’s security. And Apple has made clear it intends to win that game, no matter how badly you want to send iMessages from an Android phone.